If you came to this page without reading the introduction please go back for a brief introduction, the advantages of this method and how it works.
Use this setup if you already have a DD-WRT router in your network and plan to configure Ace VPN on it for entire house protection.
Requirements
- Ace Premium SSL VPN account or Ace Ultimate SSL VPN account
- Router running Tomato firmware with VPN mod.
- If you do not have a router flashed with Tomato. Please flash it first with the Tomato VPN build with Web GUI by SgtPepperKSU and continue with the instructions. Check if your router is supported
Warning
- This tutorial requires basic knowledge about routers and networks. If you have no prior knowledge we suggest you to familiarize about routers and networks before you continue
- Flashing third party firmware can void your routers warranty
- AceVPN.com is not responsible for any damage to the hardware, systems, or personal injury if you do attempt this!
- Only attempt if you are confident in your skills!
Assumptions
- You have the Tomato router configured and can access Internet.
Router Configuration Steps
- Connect a PC to the Lan port of the Router
- Using your browser, login to the admin page of Router B. By default this is available at http://192.168.1.1
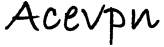
- Go to VPN Tunneling > Client Settings tab and set values as per below
- Start with WAN: Checked
- Interface Type: Tun
- Protocol: UDP
- Server Address/Port: 94.23.114.100 443
- Firewall: Automatic
- Authorization Mode: TLS
- Extra HMAC authorization (tls-auth): Disabled
- Create NAT on tunnel: Checked
Client1 > Basic tab
It would look like below screenshot when above steps are completed
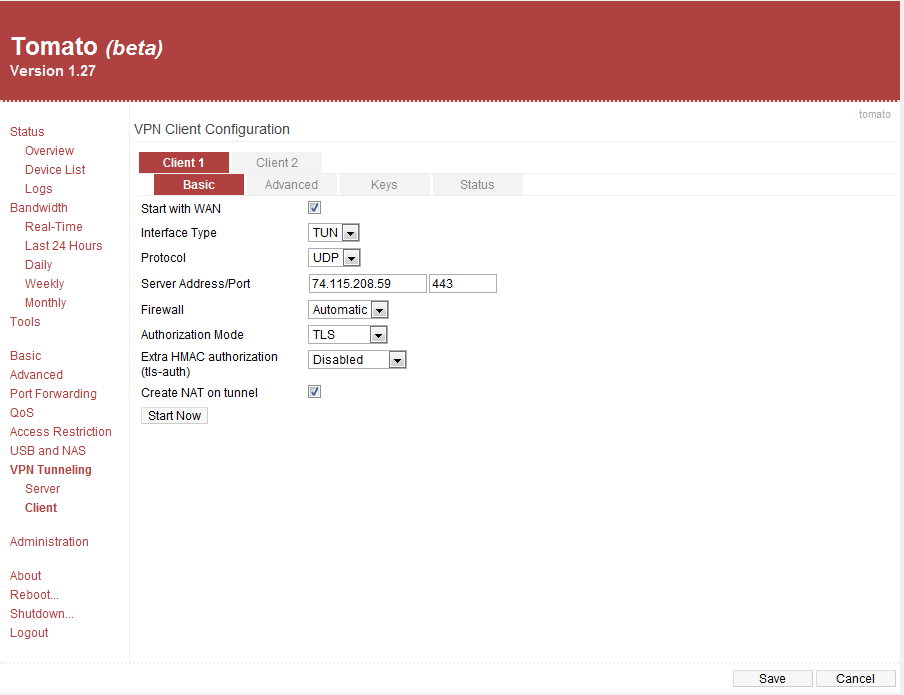
- Redirect Internet Traffic: Checked
- Accept DNS Configuration: Strict
- Encryption cipher: Use Default
- Compression: Enabled
- TLS Renegotiation Time: -1
- Connection Retry: 30
- Custom Configuration:
#NOTE: Get additional IP’s from the configuration file
remote 76.73.56.41 443
ns-cert-type server
auth-user-pass /tmp/openvpn-client1-userpass.conf
script-security 3
reneg-sec 0
Client1 > Advanced tab
It would look like below screenshot when above steps are completed
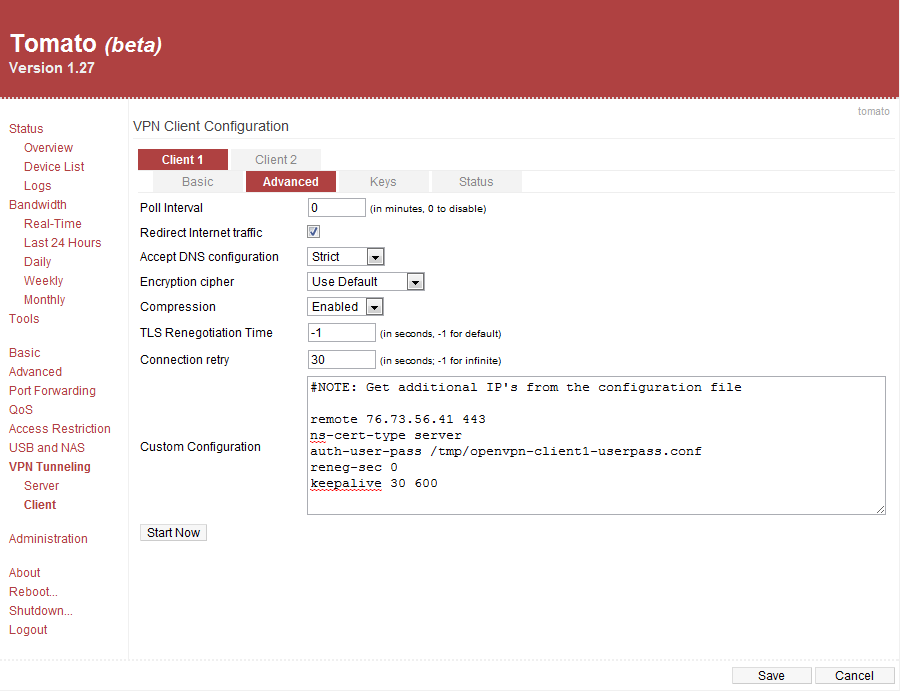
- Certificate Authority: Paste the contents of acevpn-ca.crt
- Client Certificate: Paste the contents of acevpn-user.crt
- Client Key: Paste the contents of acevpn-user.key. This is the password file. Do not share this with anyone.
- Hit the Save button to save changes
Client1 > Keys tab
It would look like below screenshot when above steps are completed
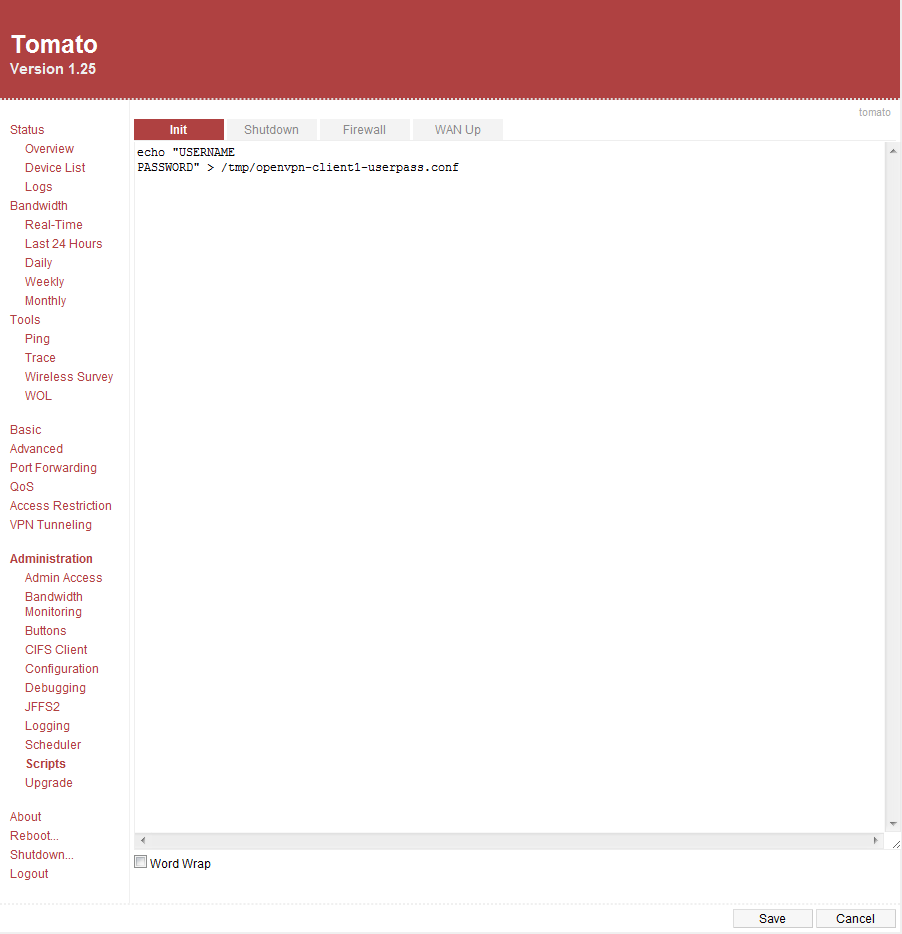
- Go to Administration > Script > Init tab and set values as per below. Replace the USERNAME and PASSWORD with the credentials you received from Ace VPN and hit Save button
echo “USERNAME
PASSWORD” > /tmp/openvpn-client1-userpass.conf
It would look like below screenshot when above steps are completed
Now reboot your router and wait for a minute for the router to establish a secure tunnel with Ace VPN gateway. Now open up a browser and go to Ace VPN home page to make sure the VPN tunnel is established.
Disconnects
If you’re unable to connect to the VPN server or can occasionally but not for more than a few minutes at a time, and you use a WAN device that does PPPoE onboard (Like a SpeedStream 5100b DSL Modem) — You may have to disable the onboard PPPoE and use the PPPoE on the WRT54G. The GRE that’s needed for the VPN sometimes gets messed up by your WAN device, probably because it uses a buggy layer 3 stack that corrupts or doesn’t pass the GRE packets to your WRT.
You may also have disconnects if the actual network that the client is on is the same subnet that the server is on (e.g. client subnet is 192.168.1.0/24 and the VPN server subnet is 192.168.1.0/24). This causes IP collisions. The best solution is to change the subnet of your client network to something unique, such as 192.168.5.0/24 (i.e. an IP range of 192.168.5.1-255 with a netmask of 255.255.255.0).
If you have additional questions or need help please contact us